Serverless Homeserver
I. Abstract
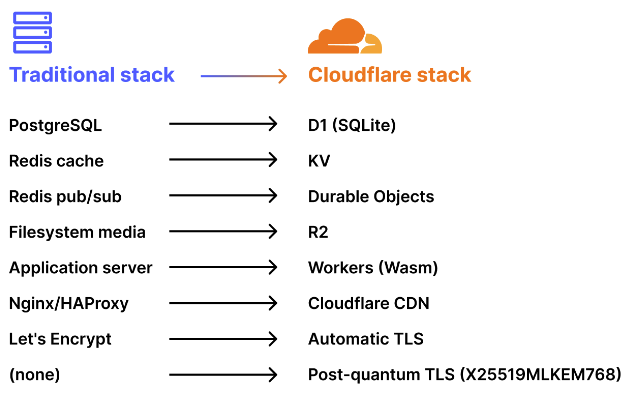
The article announces a proof-of-concept project that ports a Matrix homeserver (inspired by the reference Synapse implementation) to a fully serverless architecture using Cloudflare Workers. The goal is to eliminate the traditional operational "tax" of running a Matrix server — such as managing VPS instances, tuning PostgreSQL, handling Redis, configuring reverse proxies, and rotating TLS certificates — while delivering decentralized, end-to-end encrypted (E2EE) messaging with automatic post-quantum cryptography by default.
II. Core Implementation Details
- The core Matrix logic (event authorization, room state resolution, crypto verification) is rewritten in TypeScript using the Hono framework.
- Traditional backend components are replaced with Cloudflare's serverless primitives:
- D1 (SQLite-based distributed database) for persistent structured data (users, rooms, events — over 25 tables).
- Durable Objects for strong consistency in critical areas like one-time key (OTK) claiming, room event coordination (typing indicators, read receipts), and sync queues.
- Workers KV for ephemeral/cached data (e.g., OAuth codes with short TTLs).
- R2 for media storage with content-addressed URLs and free egress.
- Client-side Megolm encryption ensures the server never sees plaintext messages — only ciphertext is processed/stored.
- A full OAuth 2.0 / OIDC provider is included (with dynamic client registration, PKCE, RS256 JWTs, and discovery endpoints).
- Sliding Sync is supported to optimize mobile/bandwidth usage.
III. Following a Message Through the System
- A message is encrypted client-side using Megolm (Matrix's group E2EE scheme), producing ciphertext before it ever leaves the device. This ciphertext travels over TLS (terminated at the Cloudflare edge), where the Worker receives only encrypted data — never plaintext. The Worker stores the ciphertext in D1 (indexed by room and timestamp), then forwards it during syncs. Recipients receive the same Megolm ciphertext over TLS and decrypt it locally using their session keys. The server acts only as a blind relay and storage provider.
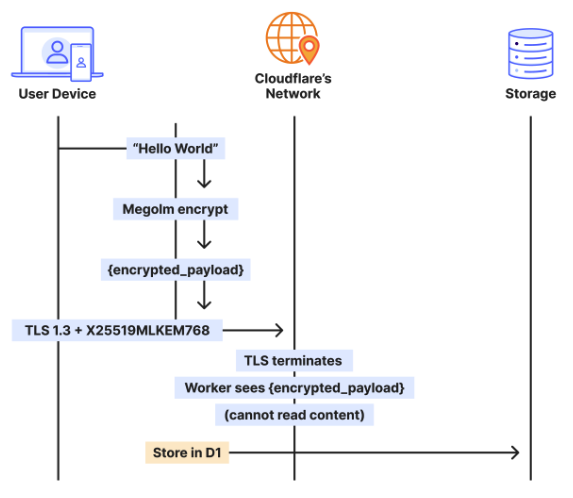
IV. Two Layers, Independent Protection
- The architecture uses two separate encryption layers for defense-in-depth:
- Transport layer (TLS) — Secures all data in transit with X25519MLKEM768 hybrid key agreement (classical X25519 + NIST-standardized ML-KEM post-quantum cryptography). Enabled automatically on all Cloudflare TLS 1.3 connections since 2022, providing quantum resistance for the channel.
- Application layer (Megolm E2EE) — Secures message content end-to-end using Curve25519-based ratcheting. Keys exist only on user devices; the server never has access.
- These layers are independent: a future break in one does not compromise the other. The server sees metadata (who messages whom, timestamps, etc.) but never plaintext content.
V. Key Benefits Highlighted
- Ultra-low latency (20–50 ms globally vs. 100–300 ms on traditional VPS) thanks to execution in 300+ Cloudflare edge locations.
- Costs scale to near-zero when idle (vs. fixed 3–10/month.
- Automatic scaling, no over-provisioning, built-in DDoS/WAF protection, and zero-config TLS.
- Post-quantum security via hybrid X25519MLKEM768 in TLS 1.3 (enabled by default on Workers since 2022).
VI. Limitation
- D1's eventual consistency required removing foreign keys and enforcing integrity in application code.
- Not all Synapse features are fully ported, and federation safety (critical for a complete Matrix server) is not yet implemented according to subsequent commentary.
Z. Resource
Important